Short CV
Sebastian Pape is a security and privacy manager working at Continental Automotive Technologies GmbH. He is also a Privatdozent at Goethe University Frankfurt and (co-)founder and managing director of the Social Engineering Academy (SEA) GmbH.Sebastian successfully completed diplomas in mathematics (Dipl.-Math.) and computer science (Dipl.-Inform.) at Darmstadt University of Technology and holds a doctoral degree (Dr. rer. nat.) from the University of Kassel and a venia legendi for computer science from his habilitation at Goethe University Frankfurt. From 2005 to 2011, he worked as research and teaching assistant at the Database Group (lead by Prof. Dr. Lutz Wegner) of the Department of Electrical Engineering and Computer Science of the University of Kassel. From 2011 to 2015, he was a senior researcher and teaching assistant at the Software Engineering for Critical Systems Group (lead by Prof. Dr. Jan Jürjens) of the Department of Computer Science Department of TU Dortmund University. From October 2014 to January 2015, he also was a visiting researcher (of Prof. Dr. Fabio Massacci) at the security group of the Department of Information Engineering and Computer Science of University of Trento. From October 2018 to August 2019 he was standing in as a professor for business informatics at Regensburg University. From 2015 to 2022 Sebastian was working as senior researcher at the Chair of Mobile Business & Multilateral Security at Goethe University Frankfurt. Outlets of his research include the following Journals and Conferences:
- Computers and Security (Core Journal Ranking 2020: B, SJR 2022: Q1) [SP20cose] [SSHP21cose] [HP23cose]
- Behaviour and Information Technology (Core Journal Ranking: B 2020, SJR 2022: Q1) [HP19bit]
- Computers in Human Behavior (SJR 2022: Q1) [HP21chb]
- IEEE Access (SJR 2022: Q1) [LTNP21access]
- Mobile Networks and Applications (MONET) (SJR 2022: Q2) [PR19monet]
- ACM SIGMIS Database, the Data Base for Advances in Information Systems (CORE Journal Ranking 2020: B, SJR 2022: Q2) [HP20sigmis]
- Information and Computer Security (SJR 2022: Q2) [SBP17ics]
- Future Internet (SJR 2022: Q2) [HP20futureinternet]
- Information (SJR 2022: Q2) [PPJM20information]
- JMIR Human Factors (SJR 2022: Q2) [SPH23jmirhf]
- Healthcare (SJR 2022: Q2) [HPM23healthcare]
- AIS Transactions on Replication Research SJR2022: Q4) [PIHNKTR20trr] [PIHNKTR20trromd]
- International Conference on Software Engineering (ICSE) (CORE Conference Ranking 2021: A*) [PFBJ16icse]
- IEEE International Symposium on Mixed and Augmented Reality (ISMAR) (CORE Conference Ranking 2021: A*) [HP17ismar]
- International Conference on Information Systems (ICIS) (CORE Conference Ranking 2018: A*) [HP19icis]
- IEEE International Requirements Engineering Conference (RE) (CORE Conference Ranking 2021: A) [BP16re]
- Privacy Enhancing Technologies Symposium (PETS) (CORE Conference Ranking 2021: A) [HPR20pets] [KGPBU22pets] [BPL22pets]
- Financial Cryptography and Data Security Conference (FC) (CORE Conference Ranking 2021: A) [Pape14fc]
- Hawaii International Conference on System Sciences (HICSS) (CORE Conference Ranking 2018: A) [HP19hicss]
- Americas Conference on Information Systems (AMCIS) (CORE Conference Ranking 2018: A) [HP18amcis]
- International Conference on Information Security and Privacy Protection (IFIP SEC) (CORE Conference Ranking 2021: B) [TKPNBTR16ifipsec][HP18ifipsec][PTKSP18ifipsec][HCP19ifipsec][HPR19ifipsec][SP19ifipsec][PHK21ifipsec][HP22ifipsec]
- Symposium On Usable Privacy and Security (SOUPS) (CORE Conference Ranking 2021: B) [HPR21soupsposter][PKR21soupsposter]
- International Conference on Availability, Reliability and Security (ARES) (CORE Conference Ranking 2021: B)
- International Conference on Trust, Privacy and Security in Digital Business (TrustBus) (CORE Conference Ranking 2021: B)
News
- June 2022: The slides and talk for A Privacy Calculus Model for Contact Tracing Apps: Analyzing the German Corona-Warn-App are now available.
- June 2022: The paper Properties for Cybersecurity Awareness Posters' Design and Quality Assessment with Sunil, Marko and Vasileios based on the Deliverable "Guidelines for Enhancement of Societal Security Awareness"is published.
- April 2022: The paper A Discussion on Ethical Cybersecurity Issues in Digital Service Chains with Frederic, Sascha and Kai is published.
- March 2022: The paper A Privacy Calculus Model for Contact Tracing Apps: Analyzing the German Corona-Warn-App with David has been accepted for presentation and publication at IFIP SEC.
- March 2022: The paper "All apps do this": Comparing Privacy Concerns Towards Privacy Tools and Non-Privacy Tools for Social Media Content with Vanessa and Sascha has been accepted for publication in PoPETs.
- November 22nd, 2021: The paper on Personal Information Inference from Voice Recordings with Jacob, Leon, Saba and Stefan has appeared in PoPETs.
- October 19th, 2021: I participated in the panel EU's cybersecurity strategies at the seminar on "Data Dilemmas: Dealing with data and investigating the consequences" organized by the Arena for Journalism in Europe
- October 16th, 2021: The paper Comparison of De-Identification Techniques for Privacy Preserving Data Analysis in Vehicular Data Sharing with Sascha, Frederic and Kai was accepted for publication at ACM Computer Science in Cars Symposium
- September 28th, 2021: I was invited to the Informatik 2021 Workshop "Security, Datenschutz und Anonymisierung" to give a keynote on "Datenschutz und -sicherheit im Internet der Dinge"
- August 18th, 2021: I was invited to the IFIP Summerschool on Privacy & Identity Management to give a keynote on Serious Games for Security and Privacy Awareness
- July 12th, 2021: Proud that David succesfully defended his phd thesis, today!
- June 23rd, 2021: Just presented our paper Privacy Concerns Go Hand in Hand with Lack of Knowledge: The Case of the German Corona-Warn-App at IFIP SEC 2021.
- June 21st, 2021: Our paper The THREAT-ARREST cyber ranges platform about THREAT-ARREST was accepted at the IEEE CSR Workshop on Cyber Ranges and Security Training (CRST)
- June 11th, 2021: The poster Leech: Let's Expose Evidently bad data Collecting Habits - Towards a Serious Game on Understanding Privacy Policies (Poster) with Alexander and Michaela was accepted at SOUPS's poster track.
- June 11th, 2021: The poster Explaining the Technology Use Behavior of Privacy-Enhancing Technologies: The Case of Tor and JonDonym (Poster) with David and Kai was accepted at SOUPS's poster track.
- April 29th, 2021: Another Statement about digital contact tracing is now online.
- April 18th, 2021: The paper Maturity Level Assessments of Information Security Controls: An Empirical Analysis of Practitioners' Assessment Capabilities with Christopher, Michael and David was accepted for publication at Computers and Security.
- April 16th, 2021: The paper Investigating Privacy Concerns Related to Mobile Augmented Reality Apps - A Vignette Based Online Experiment with David was accepted for publication at Computers in Human Behaviour.
- April 14th, 2021: The paper Case Study: Checking a Serious Security-Awareness Game for its Legal Adequacy with Dennis was accepted for publication at the Journal Datenschutz und Datensicherheit.
- April 11th, 2021: The paper Explainable Machine Learning for Default Privacy Setting Prediction with Sascha, Welde and Toru was accepted for publication at IEEE Access.
- March 23rd, 2021: The paper Privacy Concerns Go Hand in Hand with Lack of Knowledge: The Case of the German Corona-Warn-App with David and Jacob was accepted for publication at IFIP SEC 2021.
- February 22nd, 2021: I passed my habilitation lecture on Fairness in Machine Learning (German) at Goethe University Frankfurt.
- January 19th, 2021: Vanessa presented our paper Investigating User Intention to Use a Privacy Sensitive Information Detection Tool at SCIS.
- January 18th, 2021: My habilitation thesis was accepted by the extended faculty council of the mathematics and computer science faculty at Goethe University Frankfurt.
- November 28th, 2020: Empirically Investigating Extraneous Influences on the "APCO" Model - Childhood Brand Nostalgia and the Positivity Bias with David has been accepted for publication at Future Internet.
- November 2nd, 2020: Open Materials Discourse accompanying the paper Re-evaluating Internet Users' Information Privacy Concerns: The Case in Japan with Ana, David, Toru, Shinsaku, Haruo and Kai online at AIS Transactions on Replications Research.
- August 19th, 2020: The paper Conceptualization of a CyberSecurity Awareness Quiz with Ludger, Alejandro and Kristian was accepted for publication at the 2nd Model-Driven Simulation and Training Environments for Cybersecurity (MSTEC).
- August 11th, 2020: The paper Systematic Scenario Creation for Serious Security-Awareness Games with Vera was accepted for publication at the 2nd Workshop on Security, Privacy, Organizations, and Systems Engineering (SPOSE).
- July 30th, 2020: The article Re-evaluating Internet Users' Information Privacy Concerns: The Case in Japan with Ana, David, Toru, Shinsaku, Haruo and Kai was accepted for publication at AIS Transactions on Replications Research.
- June 9th, 2020: The article Asset-centric analysis and visualisation of attack trees with Christopher and Andre was accepted for presentation at Gramsec 2020.
- May 6th, 2020: The article Selecting a Secure Cloud Provider: An Empirical Study and Multi Criteria Approach with Federica, Jan and Fabio was accepted for publication at Information.
- April 19th, 2020: Joint Statement on Contact Tracing
Research Interests
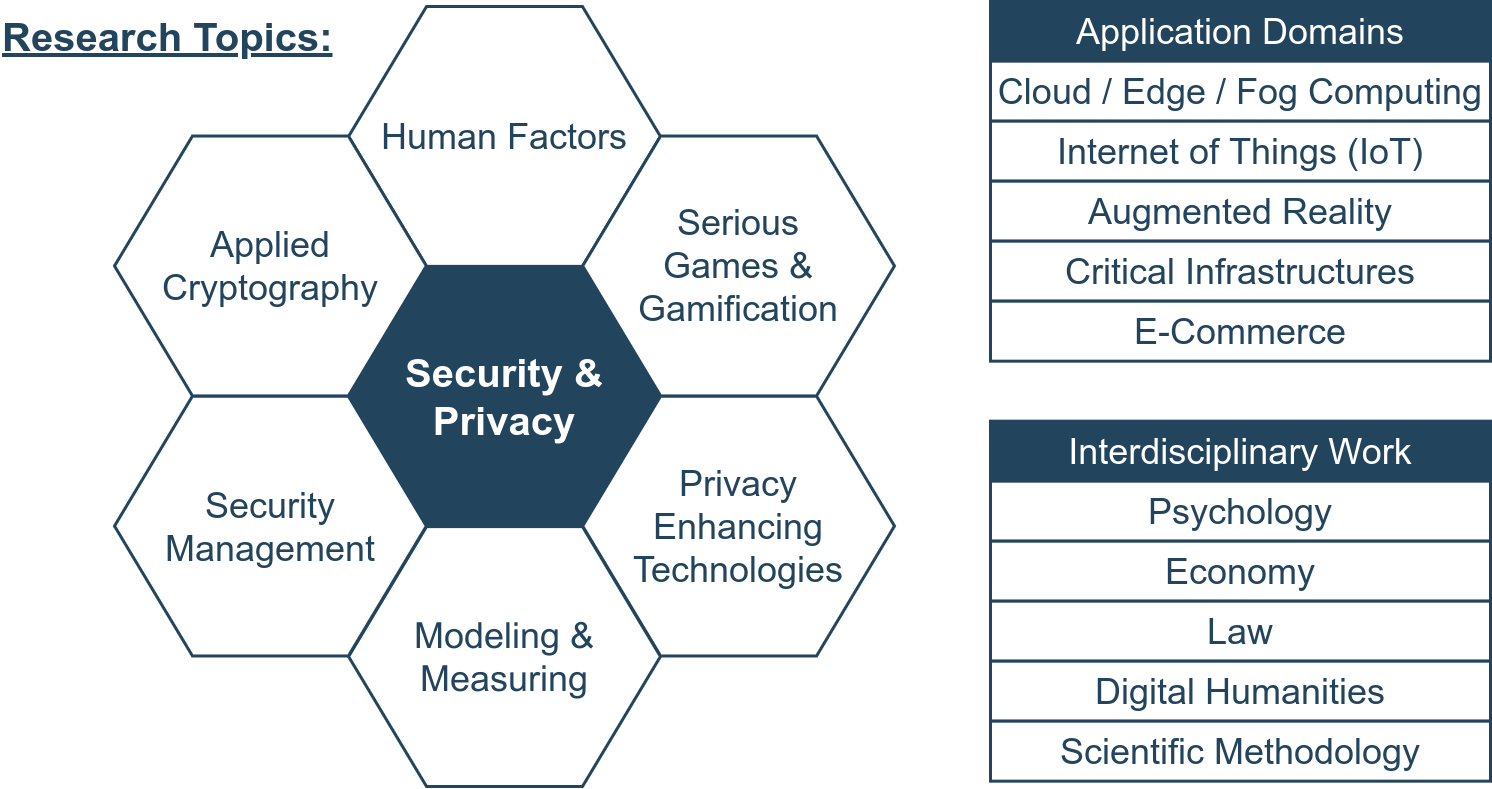

My current research focus is in the area of security and privacy with a particular interest in a holistic view on the examined systems. In particular, my research interests include, but are not limited to (naturally there will be an overlap between some of the topics):